Consumer + Provider Together: Real-World Scenarios
While Consumer and Provider are typically deployed by different organizations, there are valid
operational scenarios where the same organization deploys both:
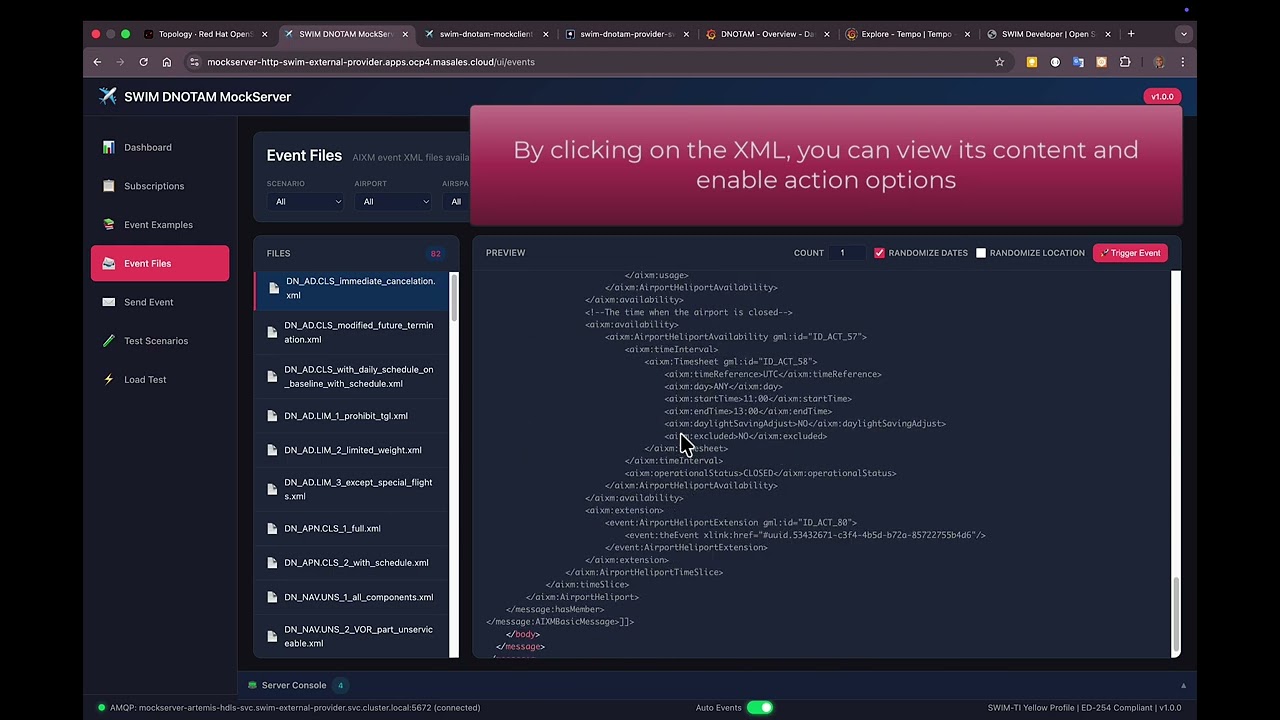
- National AIS Hub: A national authority receives events from EUROCONTROL EAD (Consumer) and redistributes to local ANSPs and airports (Provider).
- Regional Aggregator: A regional entity consolidates events from multiple national AISPs and provides unified access to regional consumers.
- Enterprise Integration: A large airline receives DNOTAM events (Consumer) and redistributes to internal dispatch centers and crew systems (Provider).
- Data Enrichment: An organization receives raw events, enriches them with local data, and republishes enhanced events.
Note: This project focuses on demonstrating technical capabilities for SWIM compliance.
The operational validity of specific scenarios should be verified with domain experts and relevant aviation authorities.
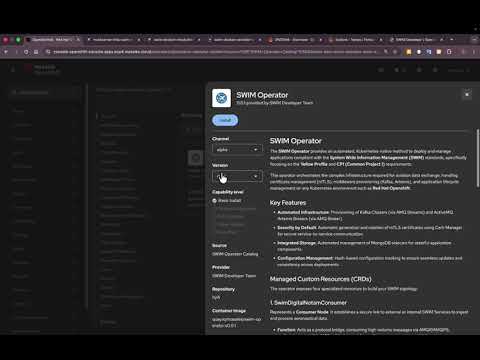
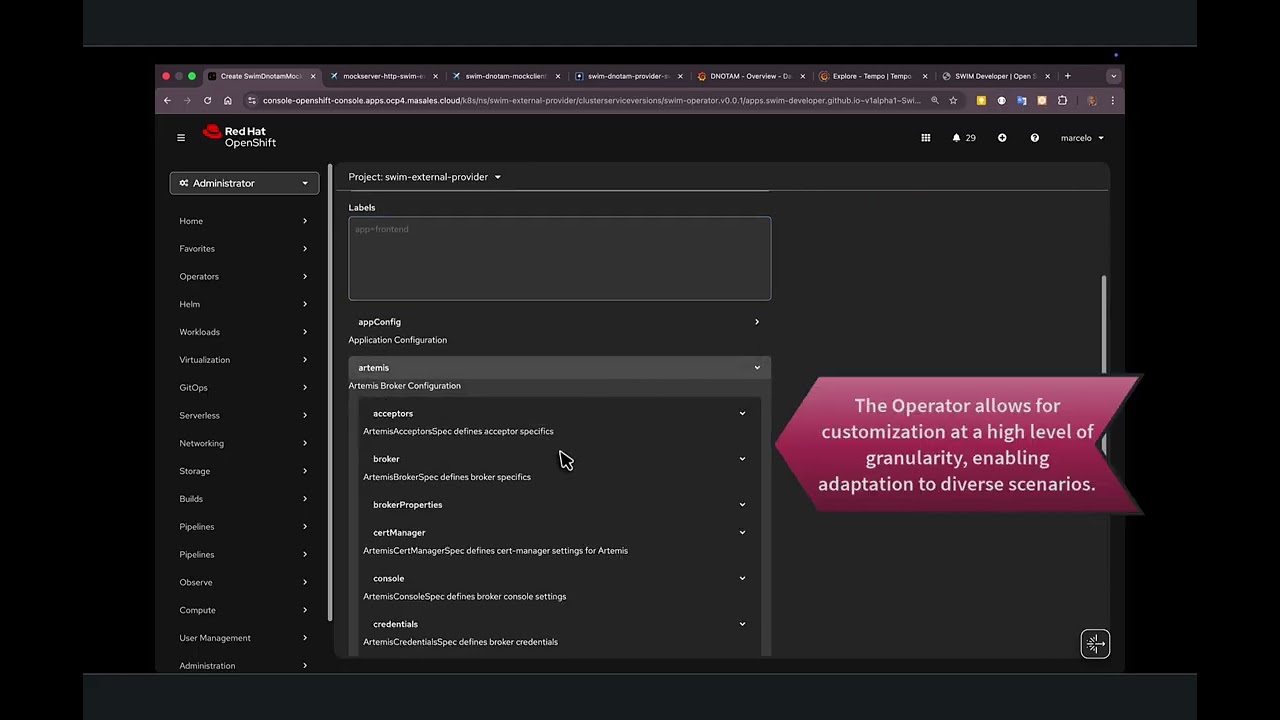
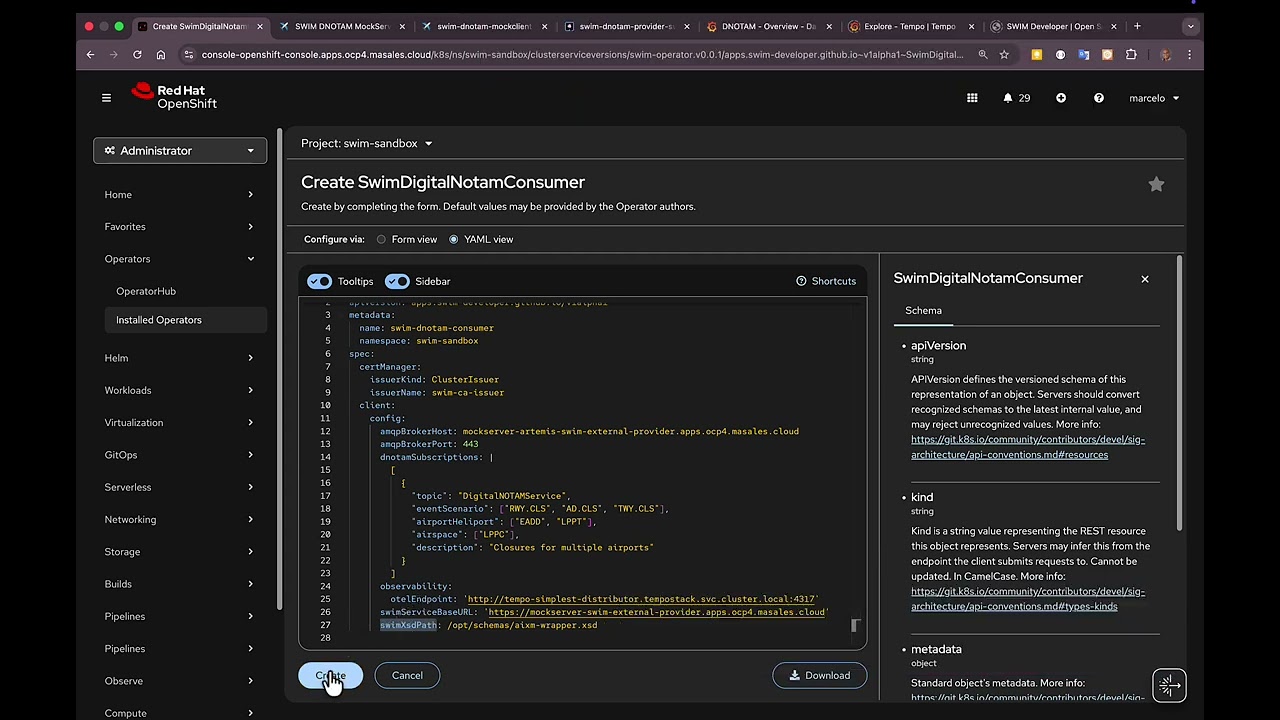
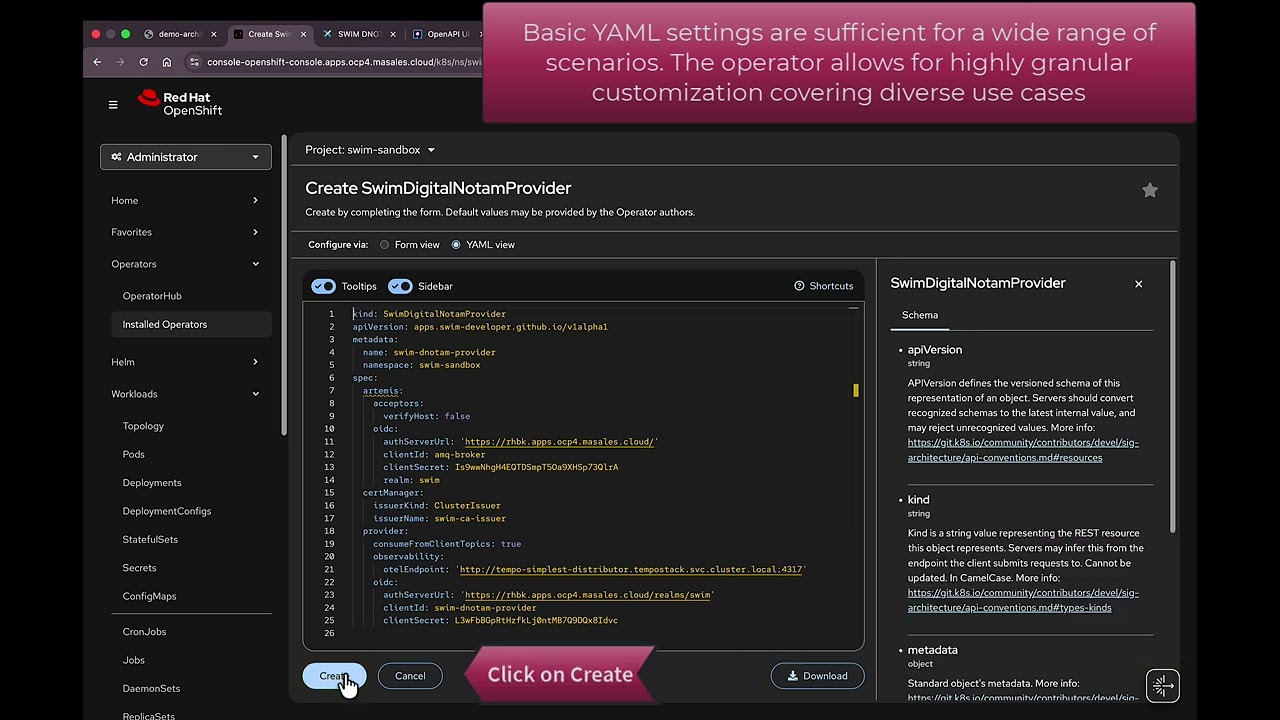
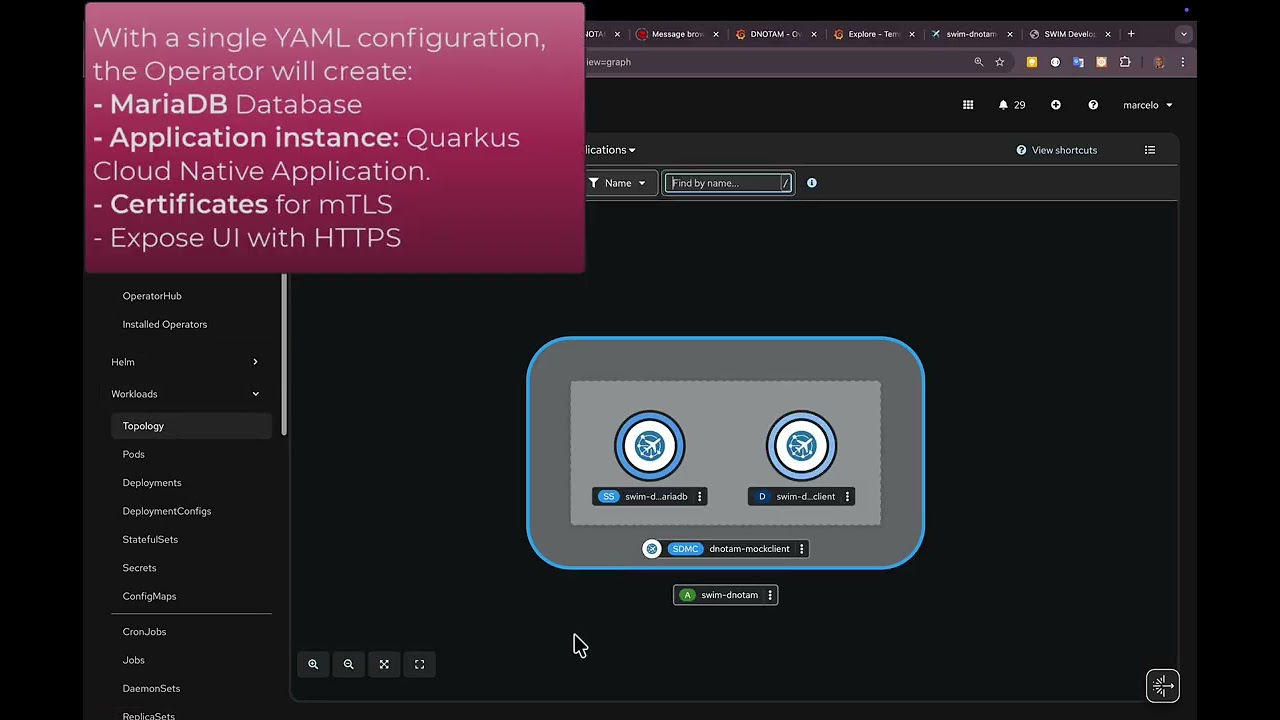
Modular by Design
Each component is an independent, containerized module. One organization can focus on the
Provider implementation—exposing SWIM-compliant interfaces and managing
subscriptions—while another develops the Consumer module for receiving
and processing events.
Both teams contribute to the same ecosystem: source code is shared on
GitHub, and container
images are published to a common registry. The result? A complete SWIM solution built
through distributed collaboration.
Open Source Collaboration
All source code is available under the BSD 3-Clause License. Organizations
are free to use, modify, and redistribute the code. Each member chooses their preferred
technology stack—as long as the container interfaces remain compatible, the modules
integrate seamlessly.
Source Code
All modules are open source. Fork, contribute, or use as reference for your implementation.
github.com/swim-developer
Container Images
Pre-built, scanned, and signed images ready to deploy on any Kubernetes cluster.
quay.io/swim-developer
Join the Effort
ANSPs, vendors, and developers can contribute modules, tests, or documentation.
See how to contribute